Permanent Roaming in IoT: Regulations, Risks, and the Right Solution (2026)
Permanent roaming works for travelers. It was never designed for IoT. Learn what permanent roaming is, which countries ban it, and what global IoT deployments need instead.
Permanent roaming works for travelers. It was never designed for IoT. Learn what permanent roaming is, which countries ban it, and what global IoT deployments need instead.
Filter articles
IoT SIM data pooling lets all your devices share one data allowance. Learn how it works, why it prevents stranded data and overage fees, and what to look for in a global IoT data pool.
IoT vendor lock-in is a technical problem, not just a contract problem. Learn where it hides, what SIM technologies reduce it, and what to look for in a connectivity provider built for flexibility.
VPN was built for users, not devices. Learn why it fails in IoT environments and how Zero Trust security eliminates the attack surface without client software.
NIS2 requires organizations to secure every network system supporting critical services, including IoT and OT devices. Here's the gap most compliance programs miss, and how Zero Trust closes it.
Utilities are deploying more connected devices than ever. Legacy VPNs widen the attack surface. Learn how Zero Trust connectivity protects smart grids, AMI 2.0, and distributed energy infrastructure.
1 in 3 data breaches now involves an IoT device. Find out why traditional IT security tools fail for connected devices, and where to apply security instead.
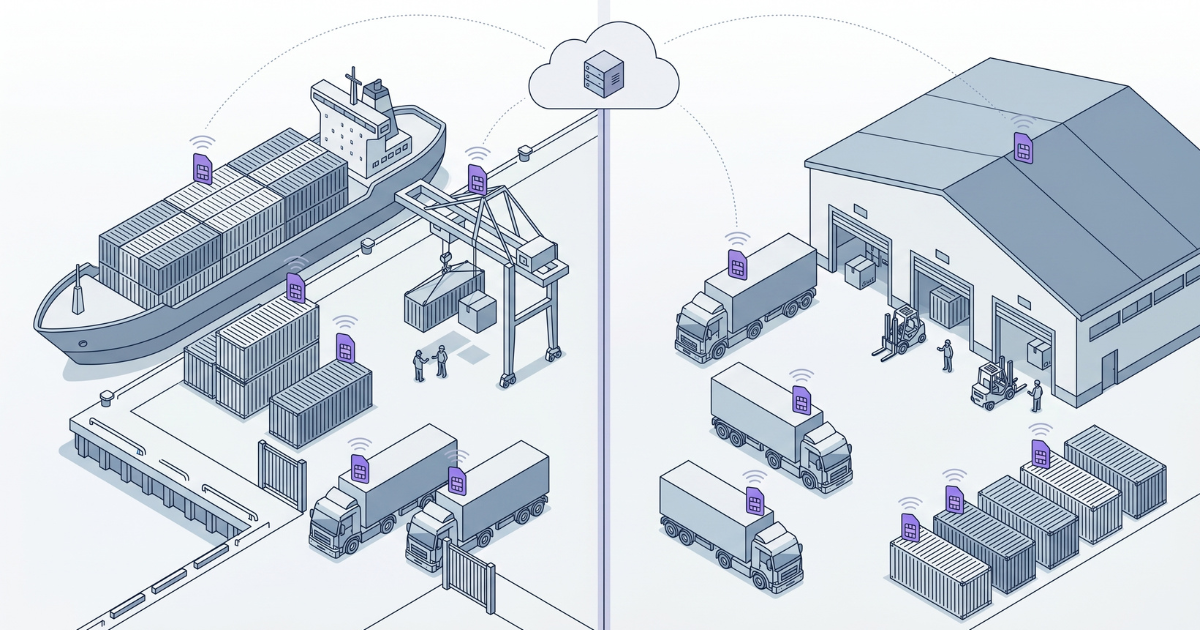
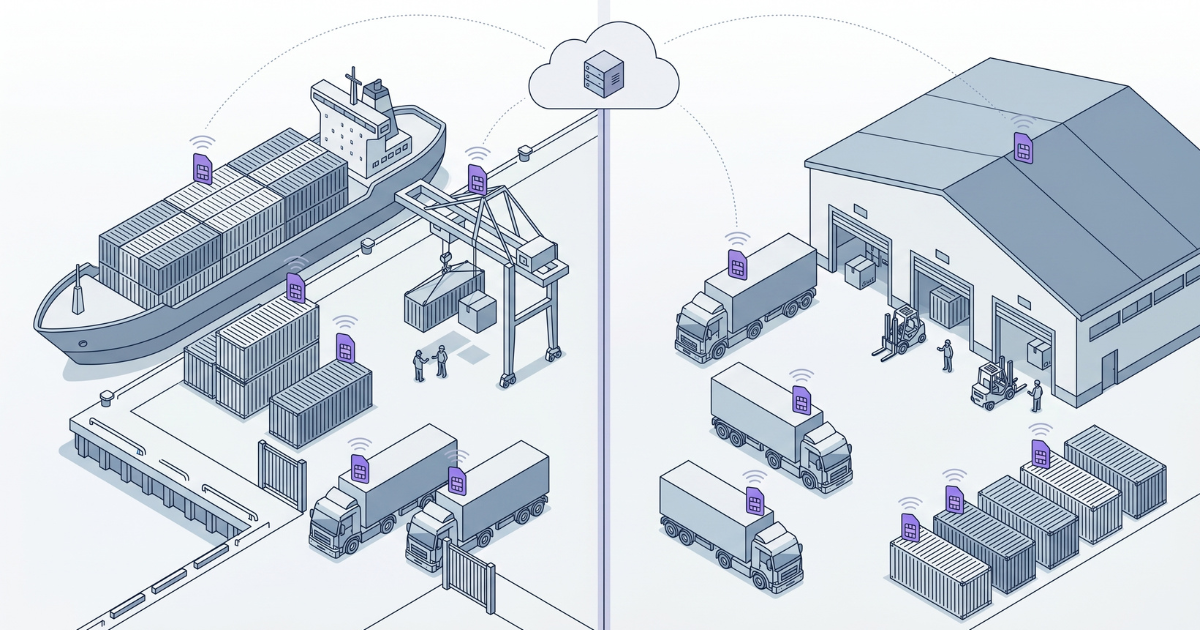
Global coverage is just a checkbox; reliability is architecture. Learn why coverage maps hide the truth about roaming bans, congestion, and network failover.
NIS2 affects how you connect, monitor, and secure IoT devices. Learn which requirements apply to SIM-based connectivity and the questions your provider should answer.