Securing IoT devices with Zero Trust architecture
Explore the essential strategies to safeguard IoT devices with Zero Trust security principles, making your connected infrastructure resilient against the ever-evolving cyber threat landscape.
IoT security can no longer rely on traditional network perimeters. This article explains how Zero Trust principles redefine device connectivity, closing the gaps left by VPNs and shared APNs.
The Internet of Things (IoT) is revolutionising various industries, from smart cities and electric vehicle (EV) charging stations to automation and utilities. However, as the number of IoT deployments increases, so does the attack surface. By 2035, it is estimated that over 50 billion connected devices will be in operation, many of which will transmit sensitive data over mobile networks with minimal or no protection. (IoT Analytics, 2025)
According to Verizon, one in three data breaches now involves an IoT device. IBM's research shows that more than 50 percent of IoT devices have critical vulnerabilities that hackers can exploit. These statistics underscore the urgent need for robust security measures to protect IoT deployments from a rapidly evolving threat landscape.
Traditional security models operate on the assumption that what is inside the firewall is safe, while what is outside is not. However, this approach is inadequate for IoT environments, which are uniquely exposed. IoT devices often sit in remote or public locations, such as municipal pump stations, EV chargers, or sensors in logistics hubs. Attackers only need to find one weak point to infiltrate a system and move laterally to reach the real target, whether it’s customer data or payment systems.
For instance, the infamous Target breach in the US occurred because attackers gained access via a third-party HVAC system vendor and then moved deeper into the company's IT infrastructure. This incident highlights the flaws in traditional security models and the need for a more comprehensive approach like Zero Trust.
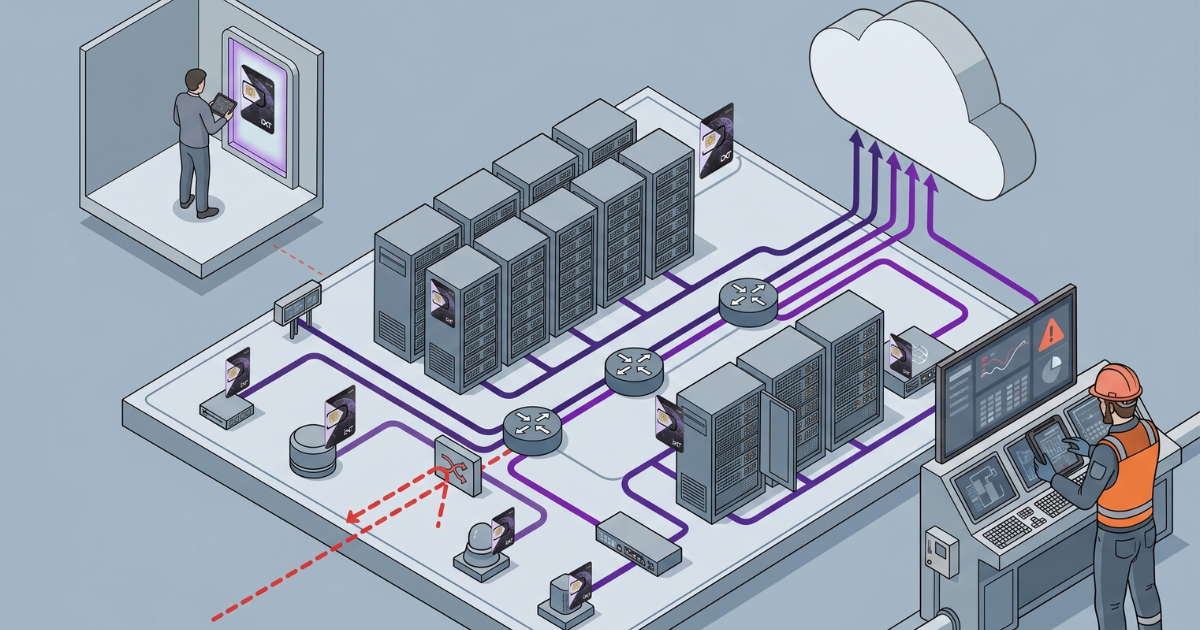
Zero Trust security is based on the principle of "never trust, always verify." Unlike traditional models that funnel devices into one broad VPN tunnel, Zero Trust takes each connection and applies strict control. Each device is identified and validated, and each request is checked against policies such as time, location, application, and patch status. Access is granted only to specific resources needed, and nothing more.
This approach removes the traditional attack surface by ensuring there are no exposed endpoints or open doors. Communication is initiated from inside-out, making it invisible to outside attackers. Zero Trust is not just a security measure; it's a paradigm shift that fundamentally changes how we protect IoT environments.
Critical infrastructures like waste management, food transport, and utilities are increasingly targeted by cybercriminals. Many of these systems were set up years ago without security in mind, making them vulnerable to state-backed actors today. Zero Trust is essential for protecting these infrastructures by providing full visibility and control over who and what is accessing devices.
For example, Zero Trust allows for granular privileges, such as limiting a vendor’s access to one sensor during a set time window while recording the session. This level of control ensures that even if one device is compromised, it does not lead to a full-scale breach.
The regulatory landscape for IoT is becoming increasingly stringent. Regulations like the General Data Protection Regulation (GDPR) and the Network and Information Systems Directive (NIS2) impose strict security standards on organisations. GDPR requires personal and usage data collected by IoT systems to be encrypted and kept within compliant jurisdictions. NIS2 expands cybersecurity duties to operators of essential services in energy, transport, health, and digital infrastructure.
Non-compliance with these regulations can result in hefty fines and reputational damage. For example, GDPR violations can reach €20 million or 4% of global turnover, while NIS2 includes stricter timelines for breach reporting and executive accountability. Therefore, adhering to these regulations is not just a legal obligation but also a critical component of a robust IoT security strategy.
Implementing Zero Trust in IoT environments may seem daunting, but modern solutions make it feasible without overhauling existing infrastructure. Here are some practical steps:
Isolated Data Paths: Use private access points (APNs) or secure tunnels to route traffic away from public networks. This prevents exposure to shared infrastructure and reduces the risk of interception or tampering.
Support for Modern SIM Technologies: Adopt solutions that include eSIM or multi-profile SIMs to ensure local compliance and resilience against permanent roaming restrictions.
Cloud-Native Integration: Direct integration with cloud environments like AWS, Azure, or GCP allows IoT data to flow securely into your backend without relying on public internet paths. This reduces latency and improves data residency control.
Network-Level Policy Enforcement: Implement a connectivity model that supports Zero Trust principles at the network edge. This includes capabilities like micro-segmentation, traffic monitoring, IP filtering, and anomaly detection as close to the source as possible.
Visibility and Management Tools: A robust connectivity management platform should provide real-time visibility into SIM usage, device activity, and connection status. Integration via APIs can simplify operations across large-scale fleets.
For organizations deploying mobile-connected IoT devices, a secure connectivity architecture should prioritize several key elements:
Isolated data paths: Utilize private access points (APNs) or secure tunnels to divert traffic away from public networks, reducing the risk of data interception or tampering.
Modern SIM technologies: Leverage eSIM or multi-profile SIMs to ensure compliance with local regulations and resilience against permanent roaming restrictions.
Cloud-native integration: Integrate directly with cloud environments to facilitate secure data flow and improve data residency control.
Network-level policy enforcement: Apply Zero Trust principles at the network edge, including micro-segmentation, traffic monitoring, and IP filtering.
Visibility and management tools: Use a connectivity management platform that offers real-time visibility into SIM usage and device activity.
As we look to the future, several emerging trends will shape IoT security and connectivity infrastructure:
iSIM goes mainstream: Integrated SIM (iSIM) technology will see broader adoption across low-power and space-constrained IoT devices, reducing hardware complexity and increasing tamper resistance.
5G RedCap deployments expand: 5G Reduced Capability (RedCap) will offer a new balance between LTE-M/NB-IoT and full 5G, enabling more critical mid-tier applications in industrial and medical IoT.
Tightening security-by-design requirements: Under regulations like the EU's Cyber Resilience Act, vendors will face stricter mandates for secure boot, OTA update integrity, and default credential policies.
AI at the network edge: AI-driven anomaly detection and policy enforcement will increasingly be run at the network edge, enabling faster threat mitigation.
Consolidation of IoT connectivity platforms: More enterprises will shift toward integrated connectivity platforms that bundle SIM provisioning, security, and policy enforcement into unified environments.
In conclusion, the Zero Trust approach is not just an option but a necessity for securing IoT deployments. By understanding and implementing Zero Trust principles, organizations can protect critical infrastructures, ensure compliance, and build a resilient IoT connectivity architecture for the future.
IXT writes about IoT connectivity because we build it. We’re a Full-MVNO with our own core network and a CMP we designed in-house, so we see what works at scale and what doesn’t. Our team has decades of experience in M2M/IoT, from network engineering to enterprise rollouts, so the guidance we share is practical, vendor-agnostic and field-tested. Connect, secure and manage devices with confidence using our IoT Connectivity.
IXT – Connected. Secure. Everywhere.
Related articles
Explore the essential strategies to safeguard IoT devices with Zero Trust security principles, making your connected infrastructure resilient against the ever-evolving cyber threat landscape.
Best practices for IoT security in critical infrastructure: private APN, encryption, zero trust, monitoring, and lifecycle management. Keep devices secure and compliant.
Learn what Zero Trust means for IoT security. Understand why traditional perimeter defenses fail connected devices and how Zero Trust principles protect your IoT infrastructure.