Permanent Roaming in IoT: Regulations, Risks, and the Right Solution (2026)
Permanent roaming works for travelers. It was never designed for IoT. Learn what permanent roaming is, which countries ban it, and what global IoT deployments need instead.
One SIM. One platform. Unlimited possibilities
Speak with Arvin – Helping Swedish Companies Simplify IoT Connectivity.
Based in Sweden, Arvin works with IoT-driven companies both locally and internationally, who are ready to modernize how they connect devices across borders. Whether you're deploying in the Nordics or scaling globally, IXT offers security, control, and ease.
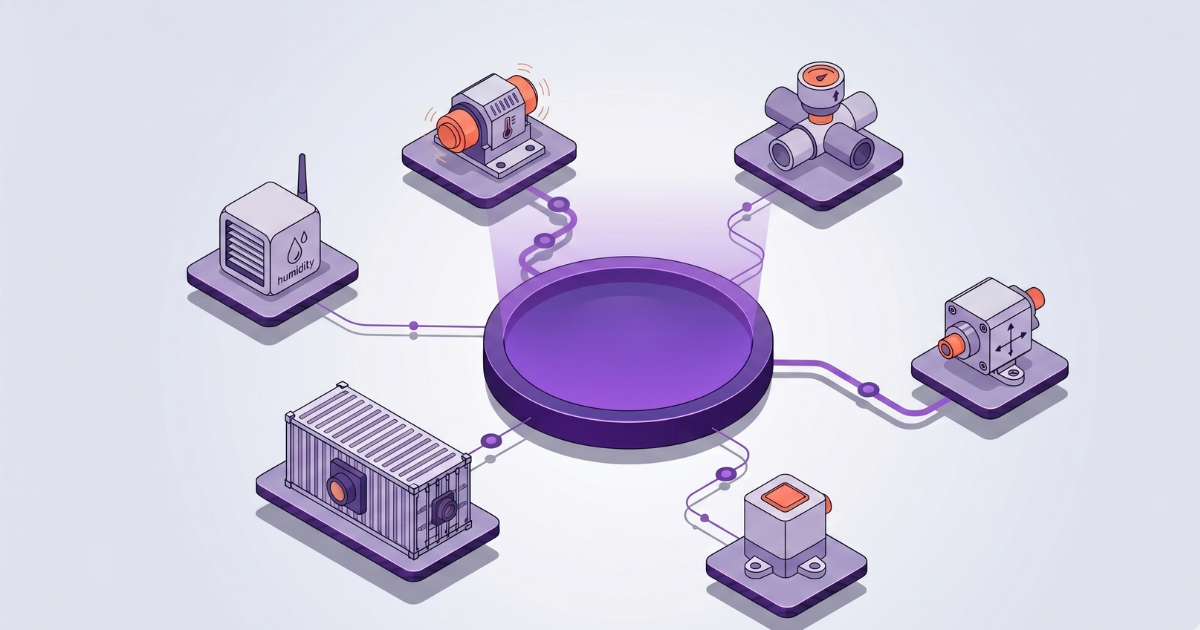
Arvin helps Swedish innovators—from OEMs to energy providers—solve challenges around SIM management, global coverage, and secure data flow. With IXT, your devices get always-on connectivity, seamless control via our CMP platform, and private, secure routing via SecureNet.
In this meeting, we’ll cover:
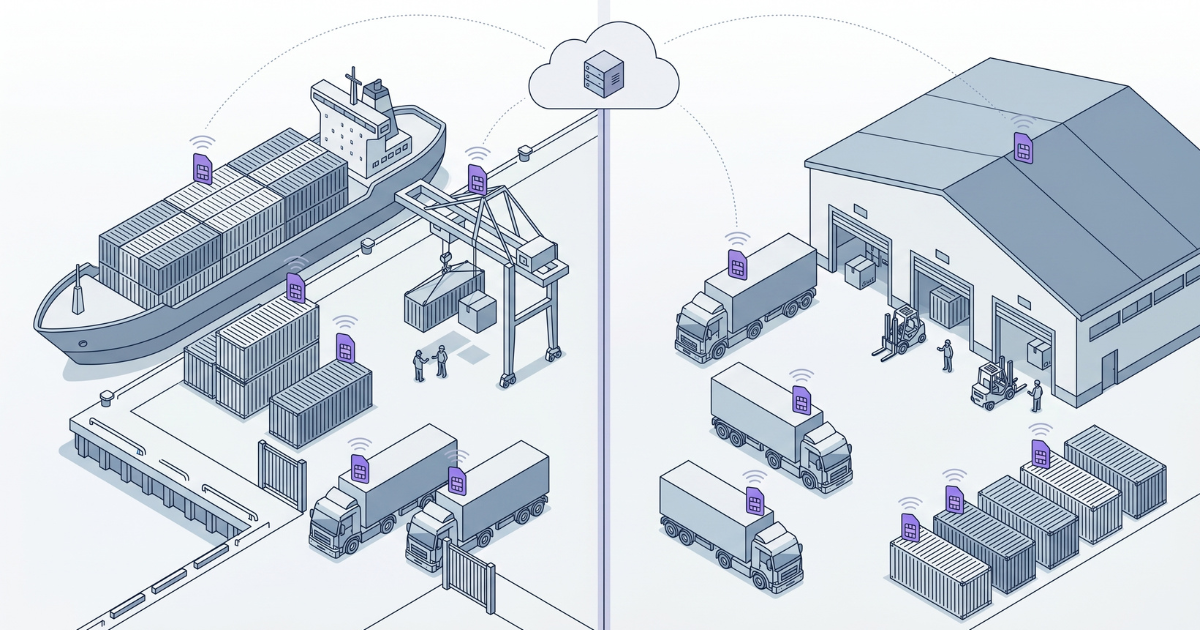
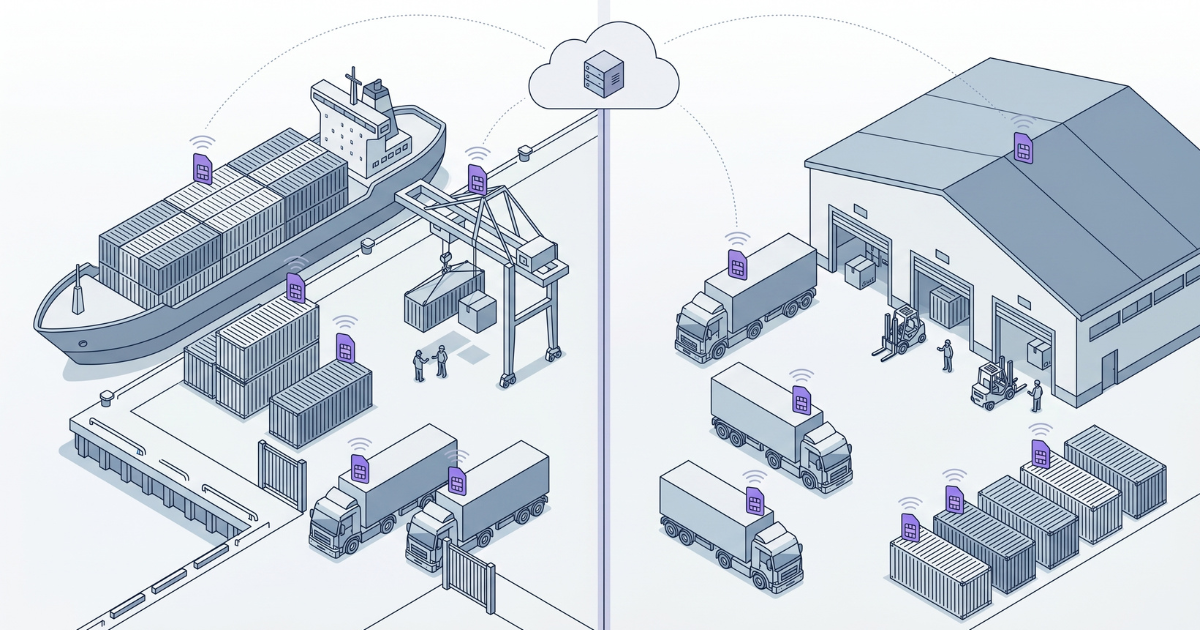
How IXT simplifies SIM deployment and lifecycle management
Your needs for scaling connectivity across geographies
Pricing and technical setup for your IoT project
Ready to streamline your SIM strategy?
Want to just contact us directly? Send an email to arvin@ixt.io.
Book a time with us
Chat with one of our IoT experts to discuss your IoT project. Book a meeting or reach out to find a suitable time.
Initial conversation
Lorem ipsum dolor sit amet, consectetur adipiscing elit.
We want to understand your specific needs and help you find the most suitable solutions—without any strings attached.
Personalised recommandation
After the meeting we will summarise our conversation for you and let you know how IXT can solve your IoT connectivity needs.
Next steps
If you want to move forward we will partner with you to tailor the best suited solution for you. If you need more time we will catch up whenever you are ready.
Explore our content
Permanent roaming works for travelers. It was never designed for IoT. Learn what permanent roaming is, which countries ban it, and what global IoT deployments need instead.
IoT SIM data pooling lets all your devices share one data allowance. Learn how it works, why it prevents stranded data and overage fees, and what to look for in a global IoT data pool.

Most IoT connectivity setups fail at scale due to fragmentation, security gaps, and rising costs. Compare providers and learn what enterprises need for global IoT success.